List Bombing
Published: Nov 19, 2025
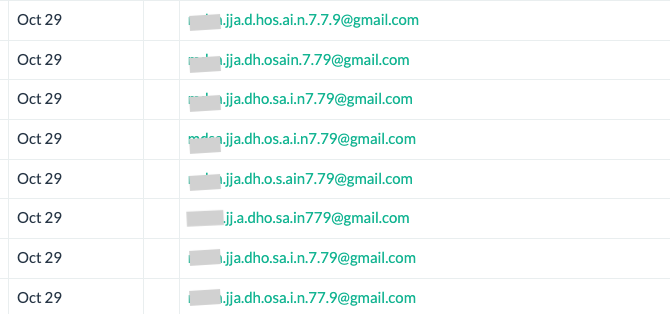
List bombing can happen to anyone who has unprotected webforms that collect emails, and can rapidly damage your sender reputation and email deliverability. This article will help you understand what it is, how to prevent it, and what to do if you were a victim of a list bombing attack.
If you are a BigMailer customer who suspects list bombing attack is in progress reach out to us via chat to see how we can help.
Always monitor your campaign engagement and strive to improve email deliverability to make the most of your email program, and to prevent any long-term performance issues.
Email Marketing Tips in Your Inbox
Only the good stuff - expert tips, best content, and no spam ever.